Introduction
Patch management in large organizations is no longer just an IT task. It is a critical part of enterprise security, regulatory compliance, and operational stability. As companies grow to manage thousands of devices across offices, remote teams, and cloud environments, applying updates manually becomes impossible.
This is why modern enterprises build patch management and compliance systems instead of relying on ad-hoc processes. These systems define how updates are discovered, tested, deployed, verified, and reported across the entire digital environment.
Understanding how these systems work is essential for technology professionals who want to move beyond execution and into architecture, strategy, and leadership roles.
Why Patch Management Matters in Enterprise Environments
Every unpatched device represents a potential security vulnerability. Publicly disclosed exploits can be used by attackers within hours of being released, which means delayed patching directly increases organizational risk.
At the same time, applying updates too aggressively can break business-critical applications or disrupt users. Enterprises must balance security, stability, and productivity.
A well-designed patch management system creates structure around this balance. It allows organizations to move quickly when risk is high and cautiously when operational impact must be minimized.
The Patch Management Lifecycle in Large Organizations
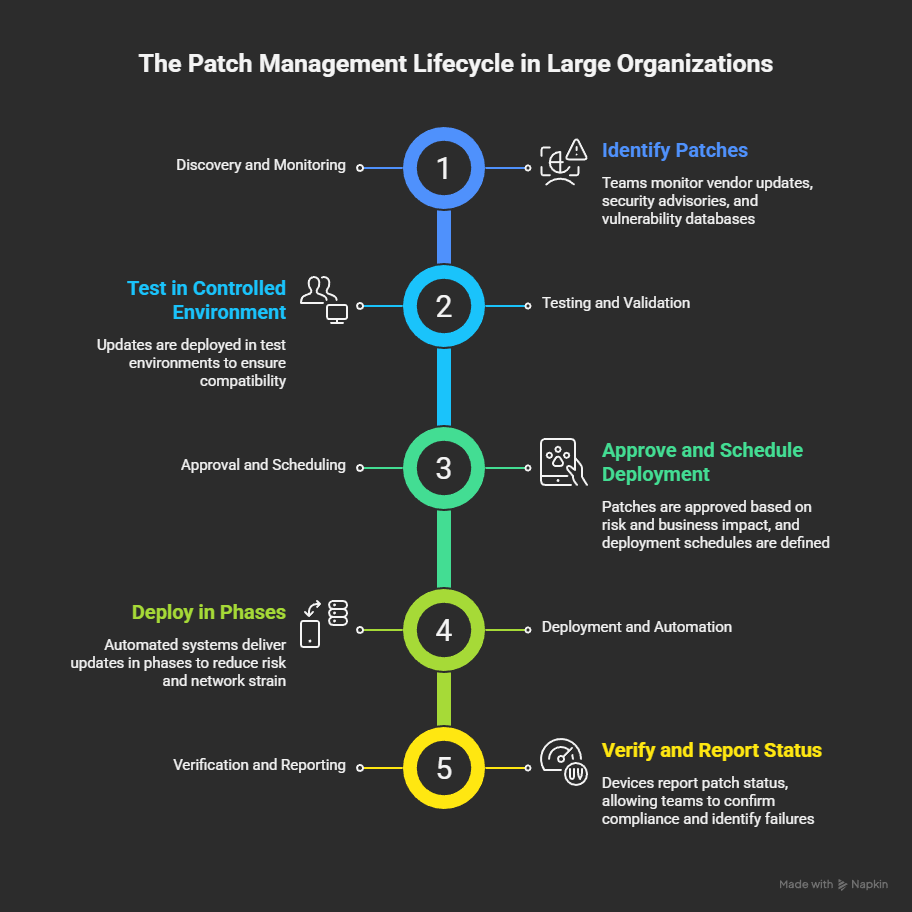
Enterprises treat patching as a lifecycle rather than a one-time event. This lifecycle typically includes five key stages.
1. Discovery and Monitoring
Teams monitor vendor updates, security advisories, and vulnerability databases to identify relevant patches.
2. Testing and Validation
Updates are deployed in controlled test environments that mirror production systems. This ensures compatibility with internal applications and configurations.
3. Approval and Scheduling
Patches are approved based on risk level and business impact. Deployment schedules are defined by department, location, or device group.
4. Deployment and Automation
Automated systems deliver updates in phases to reduce risk and network strain.
5. Verification and Reporting
Devices report their patch status, allowing teams to confirm compliance and identify failures.
This structured approach transforms patching into a predictable and measurable process.
Enterprise Patch Management System Architecture
Most large organizations build their patch management system around a central policy and control layer.
This layer defines security baselines, deployment rules, and compliance standards. Devices communicate with this system either directly or through regional distribution points to reduce bandwidth usage and improve reliability.
On top of this foundation sits a reporting and analytics layer. Dashboards provide visibility into patch compliance rates, risk exposure, and deployment trends. This data allows leadership to make informed decisions and prioritize resources based on real-world impact.
Automation as the Core of Scalability
Automation is what makes patch management possible at scale.
Automated workflows handle device enrollment, update deployment, retries, and remediation. When a device comes back online after being offline, the system can automatically assess its status and bring it back into compliance.
Phased rollouts reduce the risk of widespread disruption. Patches are first deployed to small test groups, then expanded to broader segments of the organization. This approach allows teams to detect issues early and adjust before full deployment.
Over time, these automated processes evolve into a system that reflects the organization’s operational knowledge and risk tolerance.
Compliance Reporting and Audit Readiness
In regulated industries, patch management is closely tied to compliance requirements. Organizations must be able to demonstrate that systems are maintained according to defined standards.
Effective reporting systems generate clear records showing patch status by device, department, or region. These reports support internal audits, regulatory reviews, and executive reporting.
Strong compliance visibility shifts patching from a technical discussion to a business conversation focused on risk, accountability, and continuous improvement.
Common Challenges in Large Scale Environments
Even well-designed systems face real-world obstacles.
Remote offices may have limited bandwidth, slowing deployments. Mobile or traveling devices may fall out of compliance when offline. Custom applications can conflict with standard updates.
Enterprises address these issues by building flexibility into their systems. Caching servers, alternative delivery methods, and exception workflows allow the patch management process to adapt to diverse operating conditions.
Career Impact for IT Professionals
Professionals who understand patch management systems at a strategic level gain a significant advantage.
Instead of focusing on individual updates, they begin working on policy design, risk classification, and process optimization. This often leads to roles in system architecture, security strategy, and technology leadership.
The ability to design and explain how security and compliance systems operate across an organization is a highly valued skill in enterprise environments.
Conclusion
Enterprises do not manage patches by reacting to updates. They manage them by building systems that transform constant change into a controlled, auditable, and scalable process.
These systems combine lifecycle planning, centralized control, automation, and reporting to protect both security and productivity.
For technology professionals, learning to design and improve these systems is a practical step toward building lasting digital leverage and long-term career growth.
